![PDF] SP 800-132. Recommendation for Password-Based Key Derivation: Part 1: Storage Applications | Semantic Scholar PDF] SP 800-132. Recommendation for Password-Based Key Derivation: Part 1: Storage Applications | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/92d0526c772cefb52f5309be4d0efddf7f4497f0/10-Figure1-1.png)
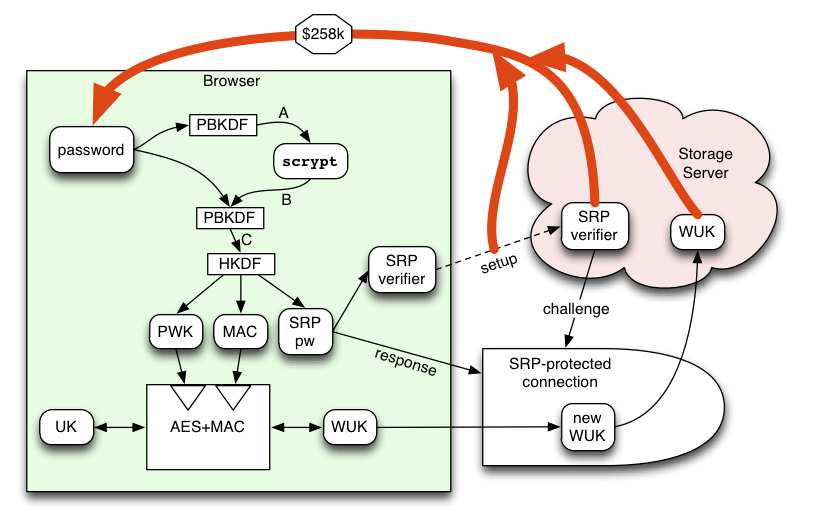
PDF] SP 800-132. Recommendation for Password-Based Key Derivation: Part 1: Storage Applications | Semantic Scholar

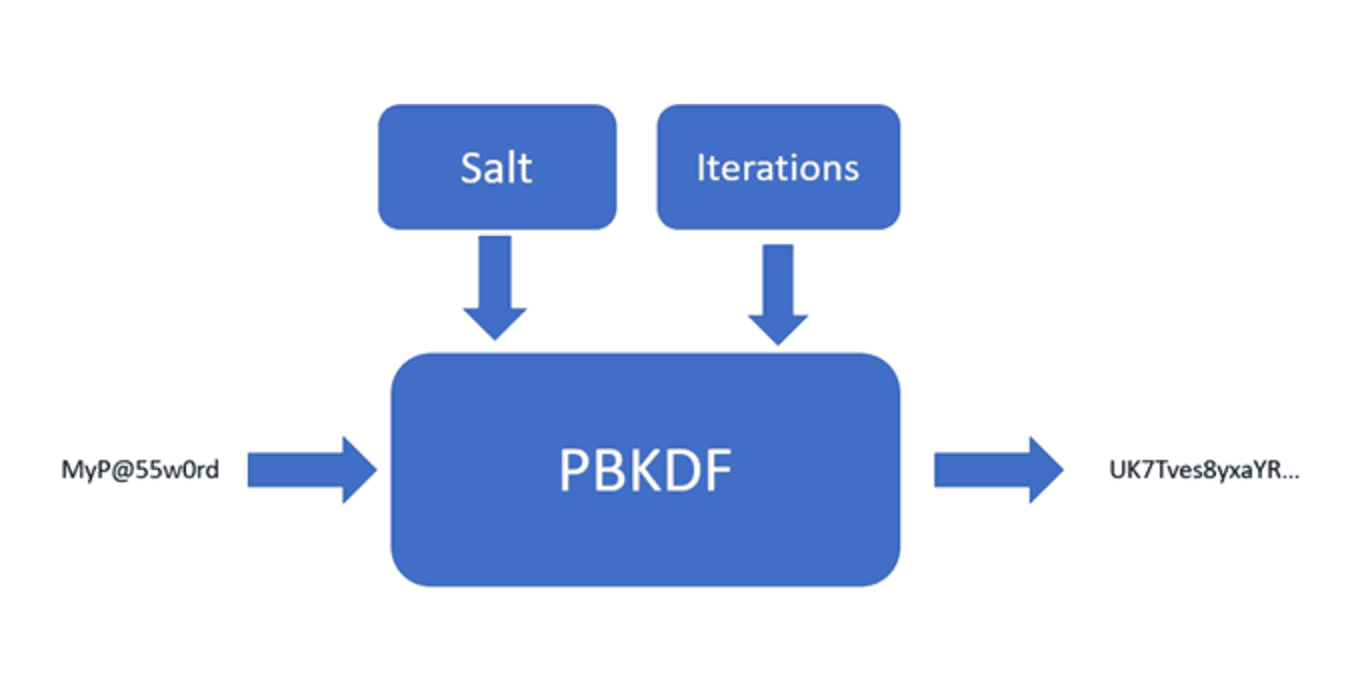
The PBKDF schematic showing the generation of a symmetric key using the... | Download Scientific Diagram
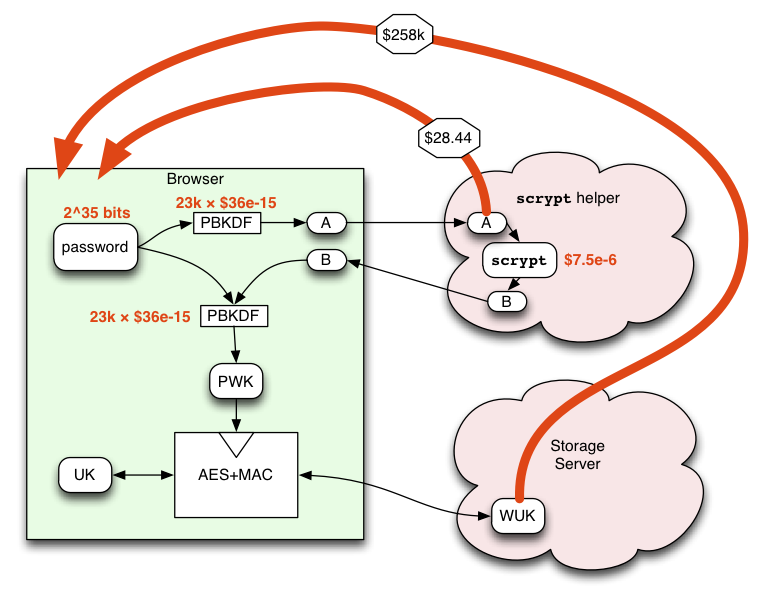
![PDF] Implementation and Performance Analysis of PBKDF 2 , Bcrypt , Scrypt Algorithms varunkrg | Semantic Scholar PDF] Implementation and Performance Analysis of PBKDF 2 , Bcrypt , Scrypt Algorithms varunkrg | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/4094a9b50ac5fd5e6d505604e667041318e5314b/6-Figure11-1.png)
PDF] Implementation and Performance Analysis of PBKDF 2 , Bcrypt , Scrypt Algorithms varunkrg | Semantic Scholar
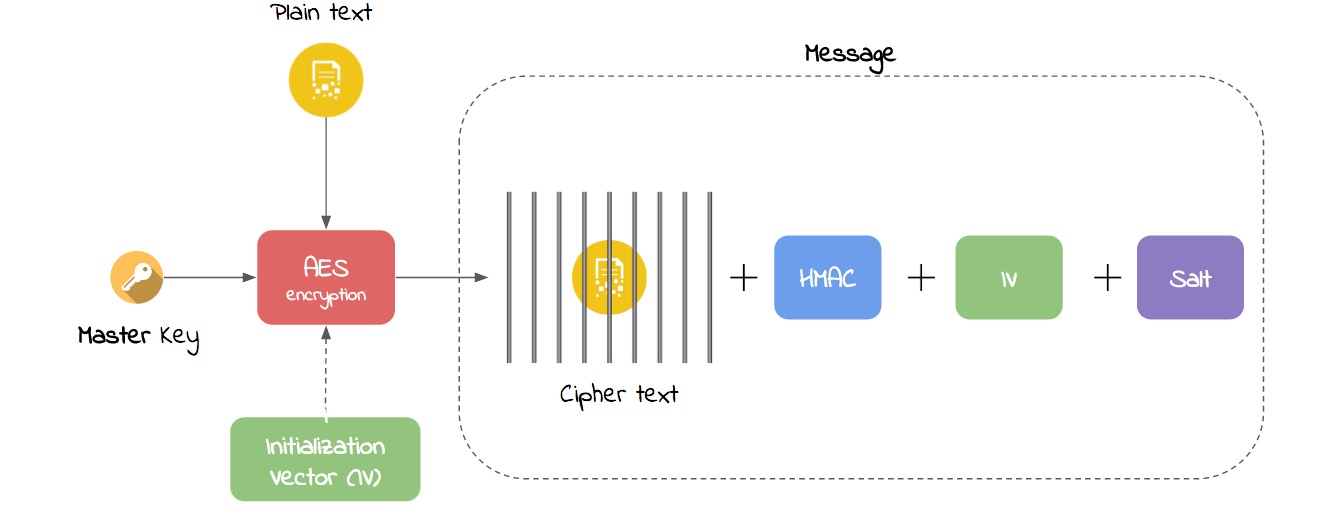
GitHub - peio/PBKDF: Password based key derivation functions (PBKDF1, PBKDF2) as defined in section 5 of PKCS#5
GitHub - juanelas/scrypt-pbkdf: A faster JS implementation of the scrypt password-based key derivation function